Much like the Emperor’s new clothes, most enterprise execution platforms parade impressive dashboards while hiding the fact that they can’t actually orchestrate work across teams with any real accountability. If you’re evaluating these systems, you need a sharper lens—one that exposes the 12 critical capabilities separating true operating systems from glorified task trackers. What follows will change how you assess every vendor on your shortlist.
Key Takeaways
- Require verifiable stage-gate governance with auditable financial outcomes, not subjective status updates or activity-based progress signals.
- Enforce role-based decisioning with least-privilege defaults, granular approval separation, and automated SLA-driven escalation paths.
- Demand outcome-linked analytics anchored to dollars delivered, not vanity activity metrics like tasks completed or meetings held.
- Ensure mobile execution is offline-capable with conflict-resolution sync, identity logging, and SIEM-exportable audit trails.
- Validate scenario planning under peak-load conditions with vendor-proven capacity envelopes, not demo-only performance claims.
Why Most Execution Platforms Fail at Orchestration
Although many platforms market themselves as enterprise execution operating systems, most fail at orchestration because they can’t enforce verifiable stage-gate governance. Meaning workflow progress isn’t reliably tied to actual outcomes but instead depends on subjective status updates that no one can audit with confidence.
When you layer in enterprise complexity, these platforms break further because they don’t map decision rights and accountability to your organization’s hierarchy. Leaving budget owner sign-off ambiguous and generating costly rework when milestones slip.
You’ll also find that most platforms treat tasks as isolated items rather than modeling cross-portfolio dependencies. So when a milestone is missed, you’re left manually tracing downstream impact through spreadsheets instead of receiving immediate, system-generated alerts that connect every affected workstream to the delay.
The strongest platforms also support aligned OKRs and governance rhythms so strategic objectives stay connected to day-to-day execution with visible accountability.
Workflow Orchestration That Spans Teams and Systems
Because enterprise execution demands coordination across dozens of teams and systems simultaneously, you need workflow orchestration that enforces multi-team, multi-system end-to-end execution with defined stage-gates, auditable checkpoints, and explicit failure behavior that dictates how downstream work responds when a milestone slips.
Every action within these workflows must be identity-aware, meaning SSO via SAML or OIDC, enforced MFA, and SCIM-based provisioning tie each step to a verified user and role for full traceability.
You should also require real-time cross-system monitoring through event exports or SIEM-friendly audit log streaming, giving leadership a single objective source of truth.
Finally, demand that orchestration produces decision-ready outputs—not just task statuses—such as instantly surfacing downstream portfolio impact and preventing phantom value closures lacking verified financial outcomes.
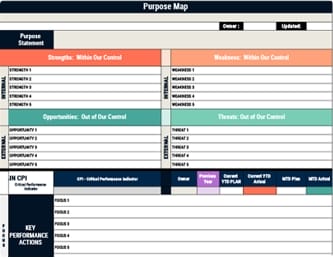
This becomes even more effective when paired with visual management tools that provide real-time transparency, clarify responsibilities, and help teams identify inefficiencies before they cascade across dependent workflows.
Role-Based Tasking With Configurable Approvals
When workflow orchestration spans multiple teams, the approval mechanisms governing each stage must be equally rigorous, which means you need role-based access control that maps directly to real job functions—budget owner, approver, controller, executor—with least-privilege defaults ensuring no one holds more authority than their responsibilities demand.
Permissions should be granular enough to separate “task create” from “task approve” so stage-gate closure depends on verified completion criteria, not informal status edits.
Every approval must capture a specific identity, role, timestamp, and decision outcome with audit logging enabled by default.
You’ll also want configurable escalation paths that auto-route stalled approvals to higher roles when SLA timers expire, and privileged actions like closing projects or modifying financial fields should block unauthorized attempts while recording them for traceability.
To keep approvals aligned with evolving company goals, teams should schedule regular reviews and use performance metrics to identify bottlenecks, accountability gaps, and needed process adjustments.
Automated Escalations and Notifications at Scale
Once approvals are locked behind verified roles and audit-ready timestamps, the next challenge is making sure nothing slips through the cracks at scale—which means your escalation engine must fire on measurable thresholds, not on someone remembering to check a dashboard.
Escalation engines must fire on measurable thresholds—not on someone remembering to check a dashboard.
You need configurable triggers for missed stage-gate dates, budget variance percentages, and p95 SLA breaches, each mapped to severity ladders with defined ownership per organizational role.
A visual management board can complement these escalations by making threshold breaches and ownership visibly clear through color-coded indicators and real-time performance tracking.
Confirm that bulk-stage events across an entire portfolio deliver within seconds-to-minutes, with retry/backoff logic and idempotent sends that prevent duplicate alerts during service degradation.
Your platform should route escalations across email, Slack, SMS, Jira, and ServiceNow through auditable rules, with dead-letter routing for failures.
Demand two-way outcomes—acknowledgement capture, reason codes, and resolution links that automatically update portfolio status for controller-ready reporting.
Mobile Execution Access for Distributed Teams
Extend your execution operating system to the field by requiring offline-capable mobile access that lets distributed teams capture work status, photos, and stage-gate updates even when cellular or Wi-Fi coverage drops, then automatically syncs those actions with conflict-resolution logic the moment connectivity returns, so no field update stalls a portfolio timeline.
Enforce role-based mobile access tied to SSO via SAML/OIDC with MFA, ensuring managers and front-line staff operate under least-privilege permissions matching their workflow authorization.
Every mobile action—check-ins, status changes, approval submissions—must log user identity and timestamp with exportability to your SIEM/SOC workflows.
Configure defined failure modes including retry/backoff strategies with user-visible sync status across regions, and validate that peak-period surges meet p95 response-time targets without breaking governance controls.
To support transparent execution across distributed operations, mobile dashboards should surface key performance indicators that align field activity with strategic goals and make progress visible for timely adjustment.
Real-Time Status and Risk Visibility
Because executive decisions stall whenever leaders must reconcile conflicting spreadsheets or wait for manually assembled status decks, your execution operating system must deliver a single auditable source of truth that replaces subjective narrative updates with quantified stage-gate checkpoints tied to verified financial outcomes. You need portfolio-wide visibility that promptly surfaces downstream impact when a milestone is missed, so decisions happen in real time rather than at the next review cycle.
Ensure explicit, system-enforced definitions for “on track,” “at risk,” and “off track” based on measurable progress signals with documented decision rights assigned to each budget owner.
Finally, require that closure recognition depends on financial impact verification—not mere activity completion—to eliminate phantom value reporting and ensure board-ready data supports rapid resource reallocation. This approach strengthens organizational alignment by connecting strategy, structure, and communication to measurable execution outcomes.
Execution Analytics Tied to Outcomes, Not Activity
Anchor your execution analytics to measurable outcomes—dollars delivered, stage-gate financial verification, strategic objectives advanced—rather than activity counts like tasks completed or meetings held, because activity metrics create the illusion of momentum without confirming that work actually produces value.
Require each workflow stage to map directly to a financial or strategic objective and define the downstream portfolio impact when a milestone is missed, so you understand variance in business terms immediately.
Separate value potential from execution progress so interventions trigger only when verified outcomes stall, not when plans merely look busy.
Finally, instrument your analytics for traceability by logging who approved what and when, ensuring outcome-linked reporting remains defensible during procurement reviews, audits, and incident response scenarios.
This approach works best when teams distinguish between broad activity metrics and Critical Performance Indicators, limiting success measures to the vital few outcomes that truly define enterprise execution.
Standardized Data Models and Configurable Reporting
Without a standardized data model underpinning your execution operating system, reporting inevitably fragments into inconsistent spreadsheets, conflicting slide decks, and one-off dashboards that no one fully trusts.
Without a standardized data model, reporting fragments into spreadsheets and dashboards no one fully trusts.
Your platform should define a structured portfolio schema—initiatives, stage-gates, owners, dates, costs, and financial outcomes—with validated fields and required metadata that keep every team’s data comparable.
From that shared model, you’ll need configurable reporting that supports board-ready views and drilldowns from portfolio to program to initiative without rebuilding dashboards for each governance question.
This structure works best when reporting is tied to performance metrics that connect strategic choices to execution outcomes and make impact measurable over time.
Insist on “as-of” snapshots and audit-ready change history so leadership sees exactly what shifted between reporting cycles.
Finally, verify the system supports standardized export and integration patterns—scheduled extracts for finance or PMO BI tools and near-real-time refresh options—so reporting stays anchored to one source of truth.
Scenario Planning for Capacity and Constraints
When you’re evaluating an execution operating system, you need to pressure-test how it behaves not just under normal conditions but at the edges of realistic demand—because a platform that performs well during demos or pilot phases can buckle once your entire portfolio of initiatives, users, and integrations hits it simultaneously.
Define your peak-load envelope with measurable inputs and require vendors to prove performance against them. Specifically, demand:
- A capacity-and-scaling model that explains whether the system scales horizontally or vertically, identifies what breaks first under load, and documents recovery time after saturation.
- Queueing and burst-handling specifications covering synchronous vs. queued processing, maximum queue depth, and retry strategies.
- Runbook-level evidence of constraint management, including enforced rate limits, concurrency caps, and real incident communication examples.
This evaluation should also confirm that the platform supports strategic alignment by keeping execution visibility connected to shared organizational objectives under stress.
Governance Controls for Permissions and Audit Trails
Because an execution operating system touches every initiative, workflow, and decision record across your enterprise, the permissions and audit trail architecture isn’t a secondary compliance checkbox—it’s the structural layer that determines who can see, change, or delete critical execution data and whether you’ll have a defensible, tamper-resistant record of those actions when an incident, audit, or offboarding event demands one.
Permissions and audit trails aren’t compliance checkboxes—they’re the structural layer protecting every decision record in your enterprise.
In a connected business model, strong governance controls also preserve the single source of truth that integrated planning depends on across departments.
Require SSO via SAML or OIDC with mandatory MFA and validate SCIM-based provisioning so offboarding revokes access automatically.
Demand granular RBAC with testable default permissions—create restricted test roles to confirm no over-permissioning exists.
Specify audit logs capturing every action with actor identity and timestamps, exportable to your SIEM, with defined retention periods.
Define explicit failure behavior: what happens to access enforcement and log integrity when your identity provider or logging pipeline is temporarily unavailable.
Open API Integration With Your Existing Stack
An execution operating system that can’t talk to the rest of your stack through open, well-documented APIs isn’t an operating system at all—it’s a silo with a dashboard.
You need REST or GraphQL endpoints plus webhooks for real-time events so your SIEM, ERP, and data warehouse integrations don’t depend on manual exports.
Validate these three capabilities before you sign:
- Bidirectional data flow — pull work items and portfolio metrics out while pushing approvals, closures, and alerts back in, using idempotent endpoints that prevent duplicate writes during retries.
- Enterprise-grade auth — SSO via SAML/OIDC, token-based authorization, and role-based API permissions that enforce least-privilege for every integration connector.
- Full auditability — every API-driven change logs actor identity, timestamp, and correlation ID, exportable to your SIEM in near real time.
Secure Deployment, Scalability, and Upgrade Paths
The platform you select must protect your data, handle surges in demand, and evolve through upgrades without forcing you to choose between security and agility.
Verify that SSO via SAML or OIDC plus MFA enforcement are standard, and that SCIM-based provisioning delivers near–real-time deprovisioning—critical given roughly 15% of breaches trace to third parties.
Confirm encryption in transit and at rest with defined TLS versions, and ask whether customer-managed keys are supported.
Demand testable SLA/SLO availability targets, explicit RPO/RTO commitments, and multi-region failover suited to promotion-driven peak loads.
Require documented p95 latency targets, rate limits, and concurrency caps so scalability isn’t theoretical.
Finally, confirm a clear release cadence with rollback procedures and real-time audit-log export to your SIEM, ensuring upgrades never silently degrade your security posture.
Frequently Asked Questions
When Tailoring a Particular Aspect of a System to the Way a Company Does Business Enterprise Software Can Provide the Company With?
When you tailor enterprise software to how your company actually operates, it provides you with auditable decision checkpoints tied to verified financial outcomes, replacing subjective spreadsheet updates with objective, enforceable workflows.
You’ll gain identity-governed controls like RBAC and SSO with MFA, consistent integration standards across multi-cloud environments, and compliance translated into testable behaviors—such as defined retention periods and disaster recovery expectations—so your implementation matches your real operational needs.
Conclusion
Think of these twelve capabilities as load-bearing walls—remove even one, and the entire structure becomes unstable under pressure. You’ve now got a clear blueprint for evaluating any enterprise execution platform, so use this checklist to expose the gaps vendors won’t highlight on their own. When you demand auditable governance, cross-team orchestration, and outcome-linked analytics together, you’re not just buying software—you’re constructing the operational backbone your strategy actually requires.